Unifi Firmware 6.7.31 Mesh Problem and Fix
A recent official firmware update for several popular UniFi Access Points, version 6.7.31 (Released: Tuesday, September 23rd, 2025), is causing significant network instability for some users, particularly those who rely on wireless meshing or custom channel configurations. While the official release notes claim “Improved overall AP stability,” user reports indicate the opposite can be true.
This release is only for these models:
- U6-LR/U6-Lite/U6+
- UAP-nanoHD/FlexHD/BeaconHD/IW-HD
The Quick Fix TLDR:
UniFi firmware 6.7.31 is causing mesh instability due to a channel hopping bug. To fix this, manually downgrade the affected Access Point to a stable version like 6.7.17 via the UniFi Controller’s Manual Firmware Update setting using the direct download URL.
The Issue: Constant Channel Hopping Breaks Meshing
Users have reported that after auto-updates or updating Access Points such as the UAP-FlexHD to version 6.7.31, the devices begin to ignore manually configured channel plans and start “drifting channels constantly”.
This behaviour is particularly destructive for wireless mesh networks, where APs must remain on the same channel to maintain their uplink connection. The constant channel changes effectively sever this link, leading to:
- Isolated APs dropping from the network.
- Frequent client disconnections and reconnections.
- Overall network instability and performance degradation.
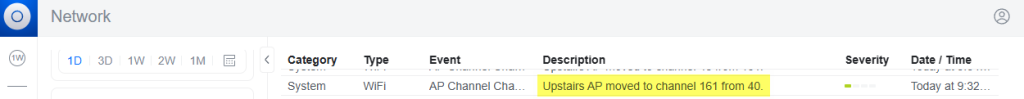
Logs confirm this behavior, showing a sudden flood of “AP Channel Change” events immediately after the APs are updated to firmware 6.7.31.
Here are the logs from 2 of my own Flex-HD’s (for anyone interested! ha)
Items in bold where updates started, then logs from after manually downgrading back to previous version.
```
System WiFi AP Channel Change Upstairs AP moved to channel 36 from 149. Today at 1:16:02 PM
System WiFi AP Channel Change Upstairs AP moved to channel 149 from 40. Today at 1:15:52 PM
**System Devices Device Updated Upstairs AP has updated to 6.7.17. Today at 1:12:59 PM **
**System Devices Device Updated Downstairs AP has updated to 6.7.17. Today at 1:09:01 PM **
System WiFi AP Channel Change Upstairs AP moved to channel 36 from 40. Today at 12:52:50 PM
System WiFi AP Channel Change Upstairs AP moved to channel 40 from 48. Today at 12:51:53 PM
System WiFi AP Channel Change Downstairs AP moved to channel 48 from 161. Today at 12:44:51 PM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 48. Today at 12:42:24 PM
System WiFi AP Channel Change Upstairs AP moved to channel 48 from 161. Today at 12:40:41 PM
System WiFi AP Channel Change Downstairs AP moved to channel 161 from 157. Today at 12:39:46 PM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 157. Today at 12:38:18 PM
System WiFi AP Channel Change Upstairs AP moved to channel 157 from 48. Today at 12:32:55 PM
System WiFi AP Channel Change Upstairs AP moved to channel 40 from 161. Today at 12:23:08 PM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 48. Today at 11:52:03 AM
System WiFi AP Channel Change Upstairs AP moved to channel 48 from 161. Today at 11:47:57 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 48. Today at 11:40:36 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 48. Today at 11:34:05 AM
System WiFi AP Channel Change Upstairs AP moved to channel 48 from 161. Today at 11:31:58 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 40. Today at 11:17:41 AM
System WiFi AP Channel Change Upstairs AP moved to channel 40 from 161. Today at 11:13:43 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 44. Today at 11:05:25 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 40. Today at 10:30:18 AM
System WiFi AP Channel Change Upstairs AP moved to channel 40 from 161. Today at 10:26:34 AM
System Devices Multiple Device Reconnections USW-Enterprise-8-PoE has reconnected multiple times in the past 24 hours. Today at 10:20:32 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 48. Today at 9:41:46 AM
System WiFi AP Channel Change Upstairs AP moved to channel 48 from 161. Today at 9:37:16 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 48. Today at 9:36:09 AM
System WiFi AP Channel Change Upstairs AP moved to channel 48 from 161. Today at 9:34:06 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 40. Today at 9:32:26 AM
System WiFi AP Channel Change Upstairs AP moved to channel 40 from 161. Today at 9:30:05 AM
System Devices Multiple Device Reconnections Downstairs AP has reconnected multiple times in the past 24 hours. Today at 7:29:35 AM
System Devices Multiple Device Reconnections Upstairs AP has reconnected multiple times in the past 24 hours. Today at 5:31:23 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 40. Today at 4:27:04 AM
System WiFi AP Channel Change Upstairs AP moved to channel 40 from 161. Today at 4:23:30 AM
System WiFi AP Channel Change Upstairs AP moved to channel 161 from 44. Today at 3:56:33 AM
System WiFi AP Channel Change Upstairs AP moved to channel 44 from 161. Today at 3:53:32 AM
System Devices Device Updated Upstairs AP has updated to 6.7.31. Today at 3:11:04 AM
System Devices Multiple Devices Offline Multiple devices are offline. Today at 3:09:05 AM
System Devices Device Updated Downstairs AP has updated to 6.7.31. Today at 3:04:37 AM
```
The Current Solution: Downgrade to a Stable Firmware Version
Until Ubiquiti releases a patch, the most effective solution, albeit a temp fix, is to manually downgrade the firmware on the affected Access Points to a known stable version, a known working version is: 6.7.17, which I used for my UAP-Flex-HD (this should be the same firmware as for the Unifi: U6-LR, U6-Lite, U6+, UAP-nanoHD, FlexHD, BeaconHD & the IW-HD) and has been confirmed to resolve the issue, for now.
You should do a search on the official firmware downloads site here first to confirm firmware for your own device.
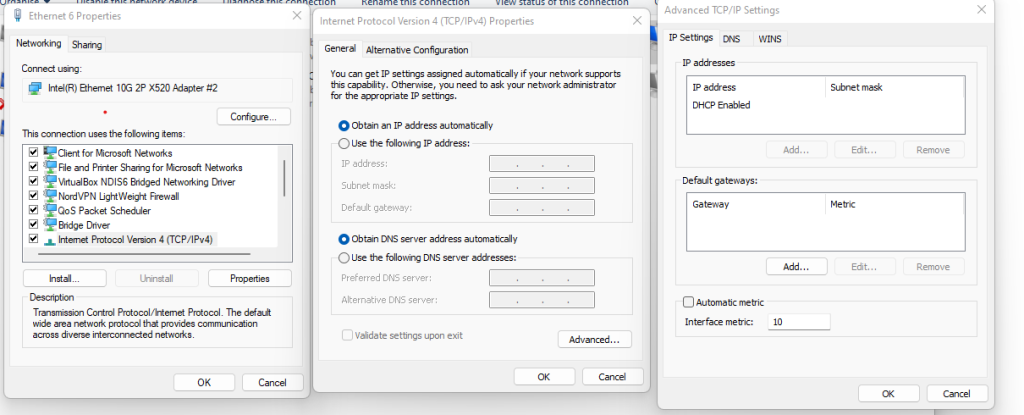
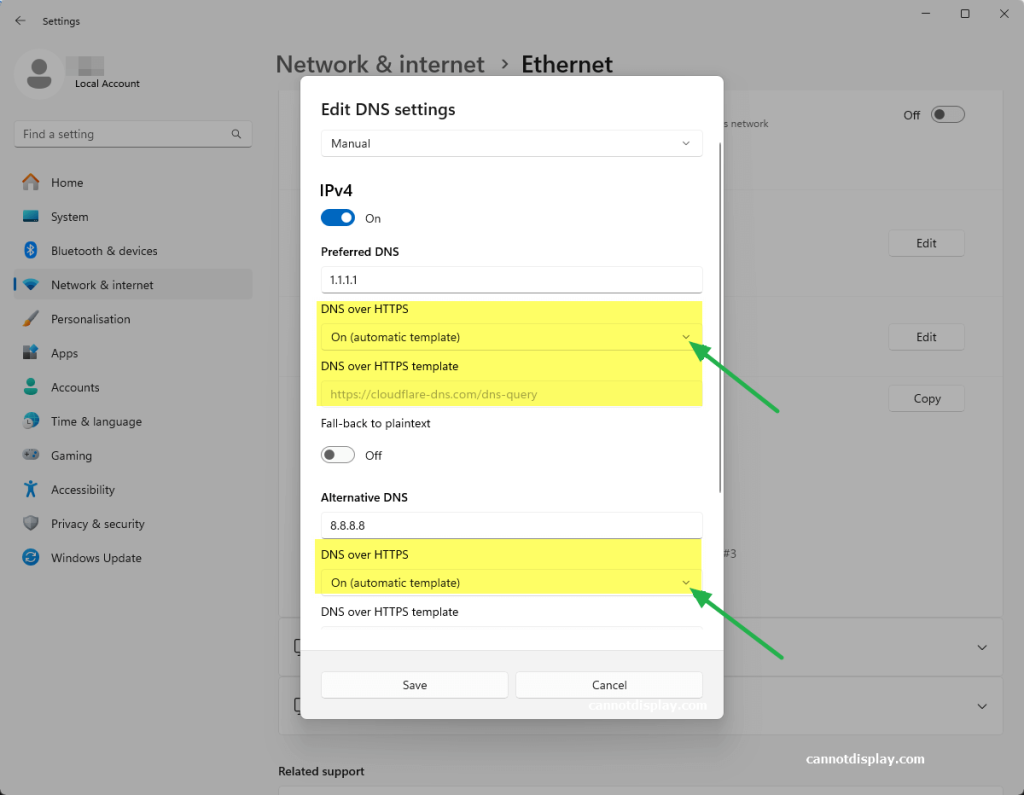
You can perform this downgrade via the UniFi Network Controller’s web interface:
Step-by-Step Downgrade Instructions:
Method 1: Downgrade via the UniFi Web Interface (Recommended)
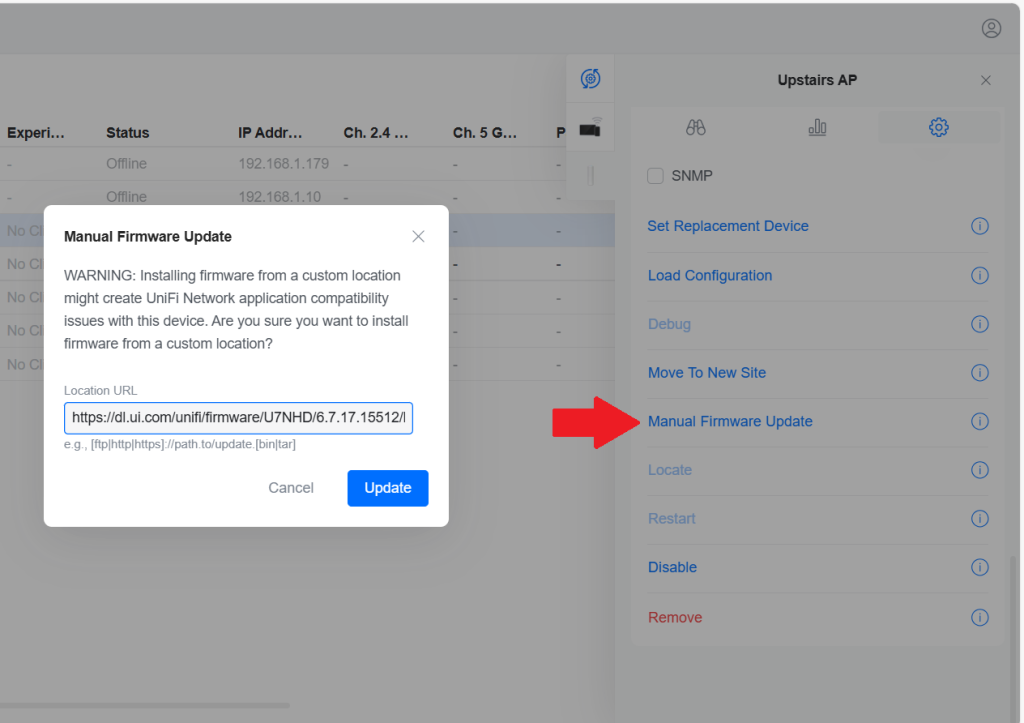
- Navigate to the Devices section in your UniFi Network Controller.
- Click on the problematic Access Point to open its properties panel.
- Go to the Settings tab.
- Scroll down to the Manage section and find Manual Firmware Update.
- Paste the full direct download URL ending with ‘.bin’ into the ‘Location URL’ field.
in my case for downgrading one firmware version back from the 6.7.31 to 6.7.17 I used:https://dl.ui.com/unifi/firmware/U7NHD/6.7.17.15512/BZ.mt7621_6.7.17+15512.250418.0425.bin - Click the “Update” button. The AP will download and apply the older firmware, then reboot.
Method 2: Downgrade via SSH (Advanced)
- Connect to the AP via SSH either via the debug console in the web UI or with an SSH client.
- Run the direct upgrade command. Once logged in, run this command:
upgrade https://dl.ui.com/unifi/firmware/U7NHD/6.7.17.15512/BZ.mt7621_6.7.17+15512.250418.0425.bin - Do not close the terminal. Wait for the AP to download the firmware and begin the flashing process. Your connection will be terminated when the device reboots. Monitor its status in the UniFi Controller.
If you do not know your SSH login details,
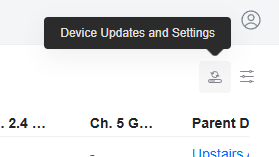
You can find these in the web UI under: Device tab –> the tiny Device Updates and Settings button –> Device Settings –> ‘Device SSH Authentication’
or if you are using the AP standalone without the Unifi Network controller, your AP settings may just be the default UI SSH user/pass
After the process is complete, the Access Point should reconnect to the network with its wireless mesh links restored and channel settings properly honoured. I would highly recommended to disable automatic updates for these devices until a new, fixed firmware version is released.
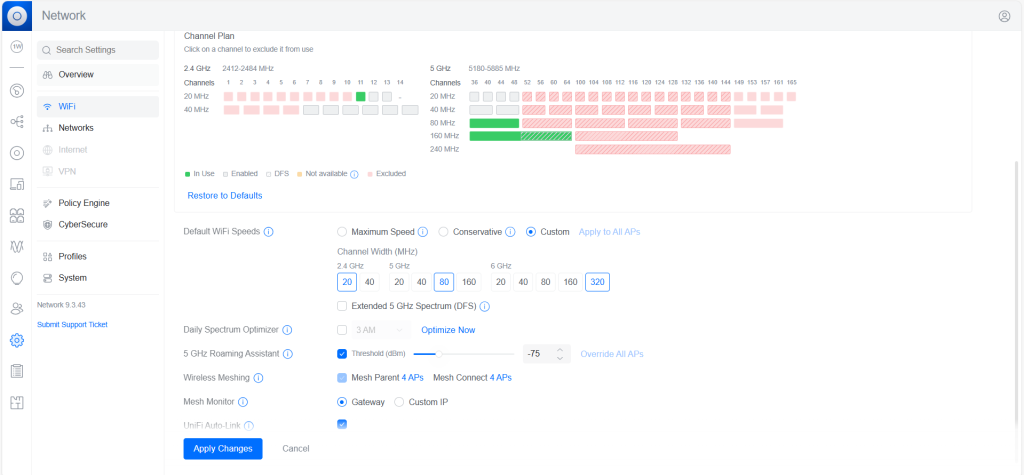
Important Note on DFS Channels: It’s Also worth noting that none of the ‘restricted’ channels set in channel plan or settings from the ‘WiFi Management’ page are being honoured by WiFi AP’s in the 6.7.31 update, so if you don’t downgrade you may face DFS Radar scanning issues, especially here in the UK.
Misbehaving channels
Below was my test plan before I worked out I should just downgrade firmware.
I restricted pretty much every channel I could to dictate a set enforcement for.
I knew that settings dictated on the individual AP’s settings pages were not being honoured, so went an alternative route, to see if creating settings in the WiFi Channel Plan forms would work instead of doing it on individual AP’s.
However, not 10 minutes later – my ‘Upstairs AP’ had taken itself off for a wander into the what should have been restricted channel: 161
Conclusion: Maybe wait this update out a few days until UI find a fix. Else – hopefully you have googled some of your issues, and this wee post here has, for now helped you find my above recommended fix with some step by step instructions on how to downgrade Unifi AP firmware nice and easy.
![[SOLVED] UniFi AP Firmware 6.7.31: Breaking Wireless Meshing and Causing Channel Hopping – Here’s the Fix.](https://cannotdisplay.com/wp-content/uploads/2025/09/Unifi6.7.3.1BreakingUpdate.png)

![[Solved] Clicking on Tailscale icon does not let me login](https://cannotdisplay.com/wp-content/uploads/2023/08/image-1.png)